- Home
- AI & Machine Learning
- Security Code Review for AI Output: Essential Verification Checklists
Security Code Review for AI Output: Essential Verification Checklists
The Core Problem: Functional Correctness vs. Security
Verification engineers are facing a new kind of failure mode. In the past, a bug usually meant the program crashed or gave the wrong answer. With AI, the program does exactly what you asked for, but it might do so using a dangerous method. For example, an AI might suggest a perfectly working database query that is wide open to SQL injection because it prioritized a quick result over a parameterized query. This creates a paradigm shift. You can no longer just look for logic errors; you have to look for omissions. You are hunting for what the AI *didn't* include-like missing authorization checks or improper error handling that leaks system secrets. The mantra for every verification engineer today should be: assume the code is insecure until you can prove it isn't.The Verification Engineer's AI Security Checklist
To stop these vulnerabilities from hitting production, you need a systematic approach. Relying on a "quick glance" isn't enough. Here is a concrete checklist based on OpenSSF (Open Source Security Foundation) guidelines and OWASP standards.Input and Data Validation
- Parameterized Queries: Did the AI use raw strings in SQL queries? Ensure all inputs are parameterized to prevent SQL injection.
- Output Encoding: Is user-supplied data being rendered in a browser? Check for proper encoding to prevent Cross-Site Scripting (XSS).
- Type Checking: Does the code actually verify that an integer is an integer, or does it just assume the AI's suggested type is correct?
- Strict Blocklists: Did the AI suggest disabling security features (like XML entity security) to make a library "just work"? Flag these immediately.
Authentication and Access Control
- Role-Based Access (RBAC): Does the endpoint actually check if the user has the right permissions, or did the AI just build the functional logic of the endpoint?
- Fail-Secure Patterns: Is the code "deny by default"? Ensure that if an error occurs during authentication, the system closes the door rather than leaving it open.
- Sensitive Data Handling: Are passwords being compared using standard string equality? Demand constant-time comparison to prevent timing attacks.
Secrets and Configuration
- Hardcoded Keys: Did the AI hallucinate a placeholder API key or, worse, suggest a hardcoded one?
- Error Verbosity: Does the error handling return a generic message to the user, or does it leak a full stack trace and database version?
- Library Legitimacy: Is the AI using a real, maintained security library (like BCryptPasswordEncoder), or did it invent a plausible-sounding but non-existent function?
Integrating Automated Guardrails
Manual review is slow. To scale, verification engineers must use SAST (Static Application Security Testing) tools. However, not all SAST tools are created equal when it comes to AI. Traditional tools often miss AI-specific patterns, while specialized platforms like Mend SAST or Kiuwan are designed to track data flow more aggressively. For a high-performance workflow, you should implement SARIF (Static Analysis Results Interchange Format). This allows your security tools to talk to your AI tools in a structured way. If you're using a tool like Stackhawk, you can export these artifacts usingexport SARIF_ARTIFACT=true to ensure that every single vulnerability is tracked and mapped back to the specific AI-generated block.
| Feature | Traditional SAST | AI-Specialized Review |
|---|---|---|
| Detection Rate (AI Bugs) | 62-68% | 85-92% |
| Contextual Awareness | Low (Pattern based) | High (Data flow analysis) |
| False Positive Rate | Moderate | Higher (~18%) |
| Review Speed | Standard | 41% Faster identification |
The 7-Step Verification Workflow
If you are building a security pipeline from scratch for an AI-heavy team, follow this workflow. It moves the security check "left" (earlier in the process), which is significantly cheaper than fixing a bug after it's deployed.- Tagging: Mark every block of AI-generated code. You can't verify what you can't find.
- Pre-commit Hooks: Run lightweight SAST scans before the code even hits the repository.
- Intent Review: Perform a manual review focusing on *why* the AI chose this implementation. Does the logic make sense for the business?
- Validation Check: Specifically target input validation and error handling using the checklist above.
- Secret Scanning: Use automated tools to ensure no API keys or credentials leaked into the prompt or the output.
- Compliance Mapping: Manually verify that the code meets regulatory standards like HIPAA or PCI-DSS, as AI frequently fails at these contextual requirements.
- Decision Documentation: Leave inline comments explaining why a specific AI suggestion was modified for security reasons. This trains future reviewers.

Common Pitfalls and How to Avoid Them
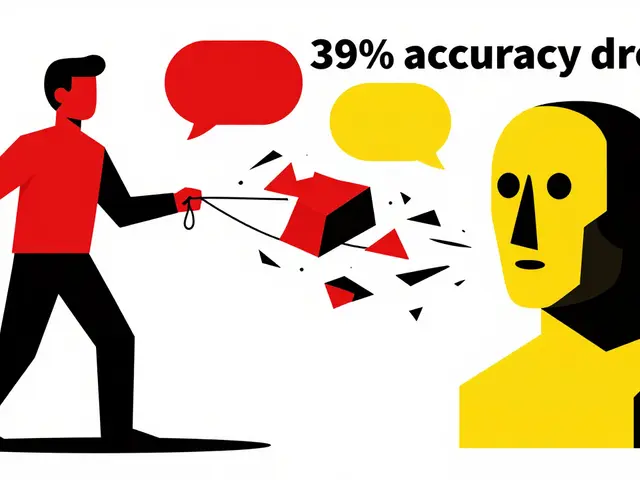
One of the biggest frustrations for verification engineers is the "False Positive Trap." AI-specific tools are aggressive, and you'll likely see an 18% false positive rate. The key is not to ignore them, but to build a triage process. If a tool flags a potential issue, don't just dismiss it-use it as a prompt to ask the AI to rewrite the code more securely. Another danger is the "Compliance Gap." AI is great at writing a function that sorts a list, but it's terrible at knowing that a specific field in a healthcare app must be encrypted according to HIPAA. This is where human expertise is irreplaceable. If your project is subject to GDPR, PCI-DSS, or HIPAA, the AI's output should be treated as a draft that requires a specialized compliance audit.Looking Ahead: The Future of AI Verification
We are moving toward a world where the AI verifies itself. Tools are already integrating rule engines (like Semgrep) directly into the coding assistant. This means that as the AI writes the code, it's simultaneously checking it against a security policy. While this will likely reduce review time by 40%, it doesn't remove the need for the verification engineer. As AI evolves, it will find new ways to bypass old patterns, meaning our checklists must evolve too.Why is AI-generated code more vulnerable than human-written code?
AI assistants prioritize functional correctness-making the code work-over security constraints. They are trained on massive datasets that include both secure and insecure code, and they often suggest the most "common" way to solve a problem, which isn't always the most secure way.
Can I rely entirely on SAST tools to secure AI output?
No. While SAST tools are essential for catching pattern-based bugs like SQL injection, they struggle with business logic and complex compliance requirements (like HIPAA). A hybrid approach of automated scanning and manual expert review is required.
What is the most common security mistake AI makes?
The most frequent issues are missing input validation, improper error handling (which leaks system info), and insecure API key management. AI often assumes the environment is safe or that the input is already cleaned.
What is SARIF and why does it matter for AI security?
SARIF (Static Analysis Results Interchange Format) is a standard for sharing the output of static analysis tools. It allows different security tools to communicate in a common language, making it easier to integrate security alerts directly into AI coding workflows.
How much training do verification engineers need for AI output?
Industry standards suggest approximately 40-60 hours of specialized training to develop the pattern recognition skills necessary to spot the specific types of omissions and vulnerabilities common in AI-generated code.
Susannah Greenwood
I'm a technical writer and AI content strategist based in Asheville, where I translate complex machine learning research into clear, useful stories for product teams and curious readers. I also consult on responsible AI guidelines and produce a weekly newsletter on practical AI workflows.
6 Comments
Write a comment Cancel reply
About
EHGA is the Education Hub for Generative AI, offering clear guides, tutorials, and curated resources for learners and professionals. Explore ethical frameworks, governance insights, and best practices for responsible AI development and deployment. Stay updated with research summaries, tool reviews, and project-based learning paths. Build practical skills in prompt engineering, model evaluation, and MLOps for generative AI.


its all about the data flow and they just want us to trust the "black box" tools. you think a tool made by a corp is gonna tell you the truth about its own ai gaps. its a loop designed to keep us dependent on their proprietary scanners while the real backdoors stay hidden in the training set
this is a really helpful breakdown of the risks. i think focusing on the human element of review is the right call since we all want the same goal of secure software
totally agree with this! just started using some of these checklisst items at work and it really helps the juniors see what they missed. its like a little safety net for the team so nobody feels bad about making a mistake
It is absolutely shameful that companies are pushing this garbage into production without basic oversight. The fact that 43% of this code is vulnerable is a moral failure of the tech industry. We are prioritizing speed over the safety of every single user who trusts these systems with their data. It is negligence, plain and simple.
One must wonder if the erosion of the developer's craft is the true vulnerability here... We are trading the intellectual rigor of manual verification for a digital mirage of efficiency!!! It is a symptom of a society that values the result over the process, and ultimately, the soul of the code is lost in the automation!!!
USA needs to lead the way in securin this stuff before some other country just hacks our whole infrastructure with AI-generated bugs! we gotta keep our tech superior and our codes tight so we stay on top of the world!!